Wireless penetration testing from Core Sentinel treats your Wi-Fi for what it really is: a door into your network that an attacker can approach from the car park, the lobby, or the building next door. We assess your wireless security the way a real attacker would — and, just as importantly, we test what they can reach once they’re connected. Every test is performed manually by a senior, certified tester. No junior bench. No scan-and-send.

Wireless is the perimeter you can’t see
Your wired network has walls and doors. Your wireless network broadcasts past them — into the street, the car park, neighbouring tenancies. An attacker doesn’t need to get inside the building to attack it; they just need to be in range. That makes Wi-Fi one of the most underestimated routes into a corporate network, and one of the most rewarding for an attacker, because a single weakness can lead straight to your internal systems.
A Core Sentinel wireless penetration test identifies the weaknesses in your wireless deployment and demonstrates their real impact — not just whether the network can be compromised, but what an attacker can do once they’re on it.
From the car park to your domain
The most damaging wireless attacks don’t stop at cracking a password. Against a corporate WPA2/WPA3-Enterprise network, an attacker can stand up an evil twin — a rogue access point impersonating your legitimate Wi-Fi — and capture domain credentials as devices try to connect.
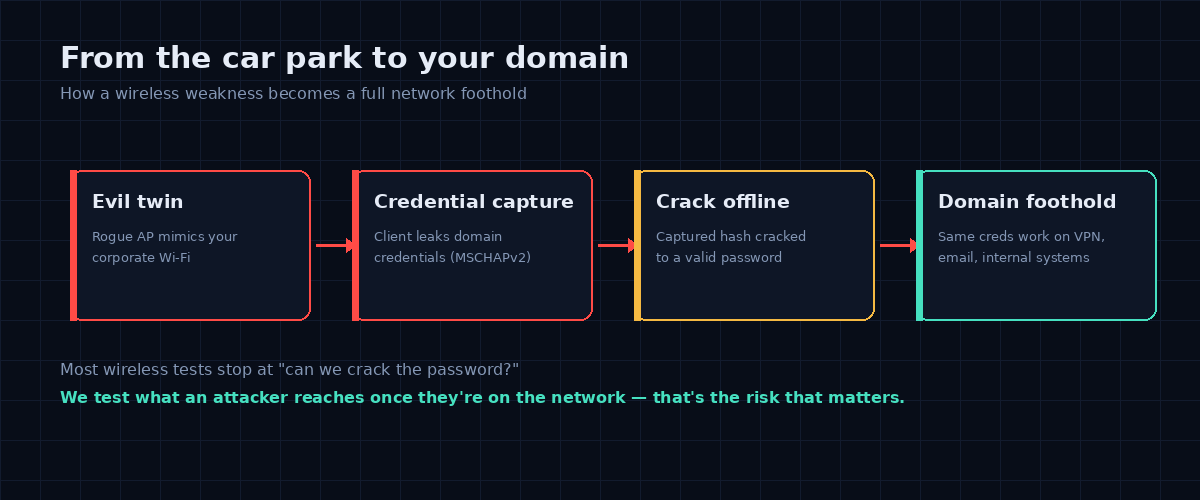
Those captured credentials can be cracked offline and are frequently valid for VPN, email and internal systems — turning a wireless assessment into a full network foothold. This is exactly the kind of chained, real-world impact a senior tester demonstrates and a checkbox scan never will.
What we test for
Our methodology covers the full wireless attack surface, with attention to the issues that matter in current environments:
- Evil twin & rogue access points — impersonating your network to capture credentials and intercept traffic, including against WPA2/WPA3-Enterprise.
- Enterprise authentication weaknesses — missing or misconfigured RADIUS server certificate validation, the single flaw that makes evil-twin credential theft possible, and weaknesses in PEAP-MSCHAPv2.
- WPA2 handshake & PMKID capture — and offline cracking of weak or guessable passphrases.
- WPA3 transition-mode downgrade — networks advertising both WPA3 and WPA2, allowing clients to be forced back to the weaker, crackable protocol.
- WPS weaknesses — PIN brute-forcing and Pixie Dust attacks that can recover the passphrase even when it’s long and complex.
- Deauthentication & client-side attacks — and whether Protected Management Frames (802.11w) are in place to prevent them.
- Rogue & unauthorised devices — unsanctioned access points creating backdoors into your network.
- Network segmentation — the critical question of what an attacker can actually reach from the wireless once connected: is guest Wi-Fi truly isolated, or bridged to sensitive systems?
- Guest & IoT networks — weak isolation and the often-overlooked devices sharing your airspace.
Senior-only testing — beyond cracking the password
Plenty of wireless tests stop at “can we get the Wi-Fi password?” That’s the easy part. The valuable findings come from a tester who can deploy an evil twin against an Enterprise network, recognise a transition-mode downgrade, and then map what that access actually exposes inside your environment. Every Core Sentinel engagement is performed by a senior, OSCE- and OSCP-certified tester who validates findings manually and rates them on real business impact.
What you receive
Our reports are written to be read — by your technical team and your executives. Every finding includes a clear risk rating, a plain-English explanation of business impact, a validated proof of concept, and a specific, prioritised remediation — from enforcing RADIUS certificate validation and moving to WPA3-only mode, to tightening segmentation so a wireless compromise can’t reach your crown jewels.
Once you’ve remediated, we re-test to confirm your risk is genuinely closed. And when we’re satisfied the risks are closed, we provide a signed letter of attestation — ready for your clients, auditors and compliance needs.
Who we work with
We test wireless networks for organisations across banking, finance, government, defence, health and education — sectors where a Wi-Fi network reachable from outside the building is a serious, often underestimated risk. Whether you’re securing a new office, a multi-site deployment, or simply want to know what’s reachable from your car park, we tailor the engagement to your environment. Wireless testing is typically conducted on-site at your premises.
Find out what’s reachable from your car park
Talk to a senior tester about your wireless security — no sales engineers, no junior hand-off. Get a quote or call 1300 859 443.