Internal infrastructure penetration testing from Core Sentinel answers the question that matters most after a breach: once an attacker is inside — through a phishing email, a compromised laptop, a stolen credential, or an exposed cloud service — how far can they actually get? We assess your internal networks and your cloud environment the way a real attacker would, manually, by a senior, certified tester. No junior bench. No scan-and-send.
Your perimeter will be breached — what happens next?
External defences matter, but they aren’t the whole story. Most serious incidents don’t end at the perimeter; they begin there. A single phished credential or one compromised endpoint gives an attacker a foothold, and from that point the damage depends entirely on your internal resilience: how easily they can move laterally, escalate privileges, and reach your most sensitive systems and data.
An internal penetration test adopts an assumed-breach mindset. We start from the position of an attacker who already has a foothold — low-level network access or a compromised account — and we determine exactly how far that foothold can be leveraged. It’s the test that reveals the risks a vulnerability scan never will.
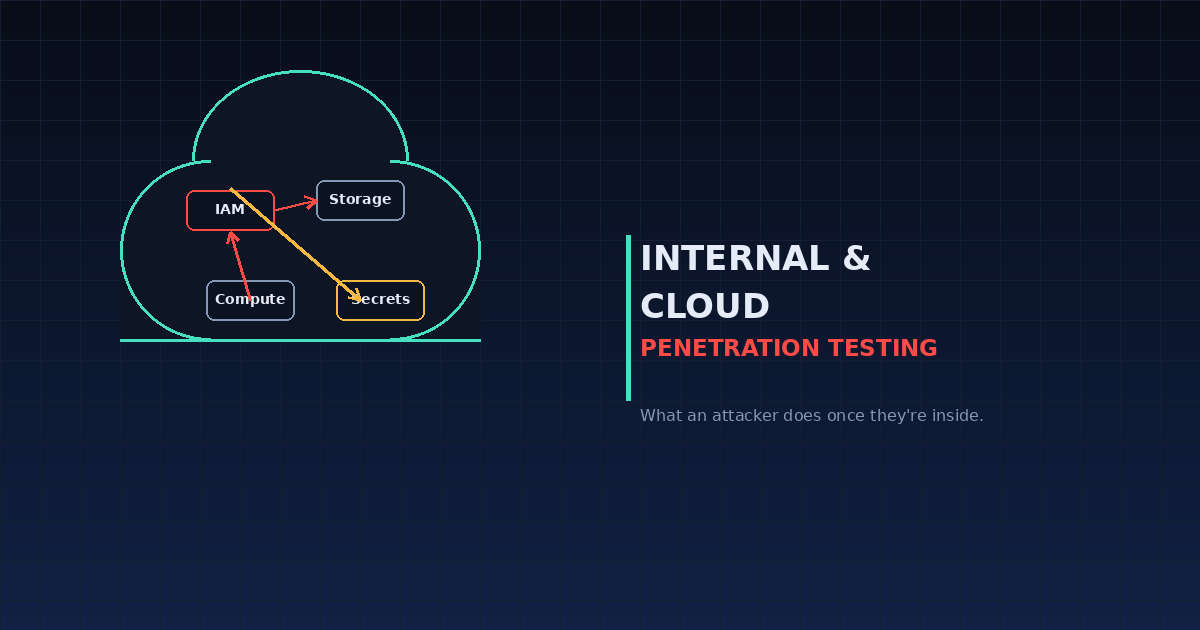
Cloud is the new internal perimeter
For most organisations today, “internal infrastructure” no longer means just a server room and a Windows domain — it means AWS, Azure or GCP. And here’s the uncomfortable truth: most organisations that have penetration-tested their web application have never tested their cloud environment. Yet that’s where the most damaging attack paths now live.
Cloud penetration testing is fundamentally different from traditional infrastructure testing. The attack surface isn’t servers and firewalls — it’s IAM policies, storage permissions, service configurations and the web of trust relationships between cloud services. An attacker who compromises a single over-permissioned function can achieve full account takeover without ever touching a server.
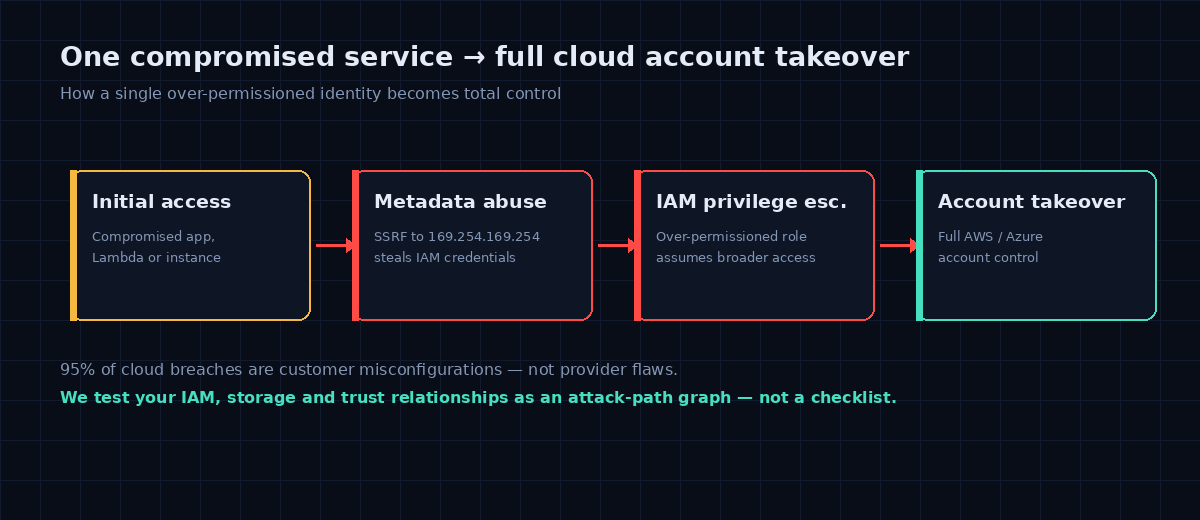
The industry figure is stark: the overwhelming majority of cloud breaches stem from customer misconfigurations, not flaws in the cloud platform itself. A permission that looks harmless in isolation becomes dangerous when combined with another. That’s why we test your cloud as an attack-path graph — mapping how identities, permissions and trust relationships chain together — rather than reviewing settings one at a time against a checklist.
What we test in your cloud environment
- IAM privilege escalation — whether any user, role or service account can chain permissions, assume roles, or abuse trust relationships to escalate to administrator-level access.
- Metadata service abuse — the SSRF-to-metadata path (the classic 169.254.169.254 attack) that turns an application flaw into stolen cloud credentials.
- Storage exposure — misconfigured S3 buckets, Azure Blob and GCS containers leaking customer data, logs, backups or credentials.
- Over-permissioned identities & secrets — wildcard policies, hard-coded keys, and credentials recoverable from compute or serverless workloads.
- Network & segmentation controls — security groups, NACLs and VPC rules that are more permissive than intended.
- Inter-service trust & lateral movement — how an attacker pivots between cloud-native services and across accounts.
- Logging & detection gaps — whether CloudTrail, GuardDuty and equivalent controls would actually see the attack.
What we test in your internal network
Where you run traditional internal infrastructure, we apply the same depth — with particular focus on the identity layer attackers prize most:
- Active Directory attack paths — misconfigured permissions and access-control entries, Kerberos and NTLM relay weaknesses, and the privilege-escalation routes that lead to Domain Admin.
- Lateral movement & pivoting — using a single foothold to reach systems and data across the network.
- Credential exposure — recoverable passwords, cached credentials and weak service accounts.
- Privilege escalation — from a standard user to local and then domain administrator.
- Trust relationships & segmentation — domain trusts, network routes and bridged networks that extend an attacker’s reach.
Senior-only testing — an attack path, not a list
This is where senior, manual testing matters most. Automated tooling can flag a thousand individual misconfigurations; only an experienced tester can tell which three of them chain into a genuine route to your crown jewels — and prove it. Every Core Sentinel engagement is performed by a senior, OSCE- and OSCP-certified tester. We manually validate every finding, build the actual attack narrative, and rate severity on real business impact rather than a tool’s default score. We also test carefully: internal and cloud environments are production systems, and we work to avoid disruption.
What you receive
Our reports are written to be read — by your engineers and your executives. You receive a clear attack narrative (the story of the highest-impact path we found, from initial foothold to maximum privilege), every finding rated by real business impact with a validated proof of concept, and a prioritised remediation roadmap with specific policy or configuration changes. Findings map to your compliance evidence needs for SOC 2 and ISO 27001.
Once you’ve remediated, we re-test to confirm your risk is genuinely closed. And when we’re satisfied the risks are closed, we provide a signed letter of attestation — ready for your clients, auditors and compliance needs.
Who we work with
We test internal and cloud infrastructure for organisations across banking, finance, government, defence, health and education — sectors where a single compromised credential cannot be allowed to become a full breach. Whether you’re securing a cloud migration, meeting a compliance requirement, or simply want to know how far an attacker could really get, we tailor the engagement to your environment.
Find out how far an attacker could get
Talk to a senior tester about your internal and cloud infrastructure — no sales engineers, no junior hand-off. Get a quote or call 1300 859 443.